SSH Remote IoT Commands: Unlock the Power of Secure Connectivity In today’s hyperconnected world, the Internet of Things (IoT) has become an integral part of our lives. From smart homes to industrial automation, IoT devices are everywhere. But with great power comes great responsibility. Securing these devices is paramount, and that’s where SSH Remote IoT Commands come into play. Imagine having the ability to control and manage your IoT devices from anywhere in the world, all while keeping them safe from cyber threats. Sounds cool, right? Well, buckle up because we’re diving deep into the world of SSH and how it can revolutionize the way you interact with your IoT devices.
Now, you might be wondering, "What exactly are SSH Remote IoT Commands?" Think of SSH as a superpower for remote access. It allows you to securely connect to your IoT devices over the internet, execute commands, and even transfer files. Whether you’re a tech enthusiast, a developer, or someone who just wants to keep their smart gadgets under control, understanding SSH is a game-changer. In this guide, we’ll break it down step by step so you can harness its full potential.
Before we dive deeper, let’s address the elephant in the room: security. IoT devices are notorious for being vulnerable to attacks. That’s why SSH is such a lifesaver. By encrypting your connections, SSH ensures that your data stays private and secure. So, whether you’re managing a fleet of IoT devices or just tinkering with your home automation setup, SSH Remote IoT Commands are your best friend. Let’s get started!
Read also:Justin Fields Why I Chose Jets
What Are SSH Remote IoT Commands?
In simple terms, SSH Remote IoT Commands are instructions you send to your IoT devices through a secure connection. SSH stands for Secure Shell, and it’s a protocol that enables you to remotely access and manage devices over a network. When it comes to IoT, SSH is like a digital Swiss Army knife. You can use it to configure settings, troubleshoot issues, and even automate tasks. The beauty of SSH is that it’s not just about sending commands; it’s about doing so securely.
Here’s why SSH is perfect for IoT:
- Encryption: All data transmitted between your computer and the IoT device is encrypted, making it nearly impossible for hackers to intercept.
- Authentication: SSH uses strong authentication methods, such as public-key cryptography, to ensure that only authorized users can access your devices.
- Flexibility: Whether you’re working on a Linux-based IoT device or a custom-built system, SSH can adapt to your needs.
For example, imagine you have a weather station set up in your backyard. With SSH Remote IoT Commands, you can log in to the device from your laptop, check the latest readings, update the firmware, and even restart the system—all without leaving your couch. It’s like having a remote control for your IoT empire.
Why Use SSH for IoT Devices?
Let’s face it: IoT devices are everywhere, but they’re not always secure. Many of them come with default passwords or lack proper encryption, making them easy targets for cybercriminals. That’s where SSH shines. By using SSH Remote IoT Commands, you can:
Enhance Security
SSH provides end-to-end encryption, ensuring that your communication with IoT devices remains private. Unlike other protocols, SSH doesn’t rely on plain text passwords, which can be easily intercepted. Instead, it uses public-key authentication, where you generate a pair of keys—one public and one private. This method is far more secure and eliminates the risk of password-based attacks.
Streamline Management
Managing multiple IoT devices can be a hassle, especially if you’re doing it manually. SSH allows you to automate repetitive tasks, such as updating software or monitoring logs. You can even create scripts to handle complex operations, saving you time and effort. For instance, if you have a network of smart sensors, you can use SSH to pull data from all of them at once, analyze it, and generate reports.
Read also:Jo Frosts Husband A Deep Dive Into Their Relationship And Life Together
Improve Reliability
SSH connections are robust and reliable, even over unstable networks. If your internet connection drops, SSH can automatically reconnect once the link is restored. This is crucial for IoT devices that need to operate continuously, such as surveillance cameras or environmental monitors. With SSH, you can rest assured that your devices will stay online and functional.
Getting Started with SSH Remote IoT Commands
Ready to dive into the world of SSH? Let’s walk through the basics of setting up SSH for your IoT devices. Don’t worry; it’s easier than you think.
Step 1: Install SSH on Your IoT Device
Most modern IoT devices come with SSH pre-installed, but if yours doesn’t, you’ll need to install it manually. For Linux-based devices, you can usually do this using a package manager like apt or yum. For example, on a Raspberry Pi, you can enable SSH by running:
sudo systemctl enable ssh
Once SSH is installed, you’ll need to configure it to suit your needs. This includes setting up firewalls, creating user accounts, and generating SSH keys.
Step 2: Generate SSH Keys
Public-key authentication is the backbone of SSH security. To set it up, you’ll need to generate a pair of keys on your local machine. Here’s how:
- Open a terminal and run:
ssh-keygen -t rsa -b 4096. - Follow the prompts to save the keys and set a passphrase (optional but recommended).
- Copy the public key to your IoT device using:
ssh-copy-id user@iot-device-ip.
That’s it! Your device is now ready to accept secure connections.
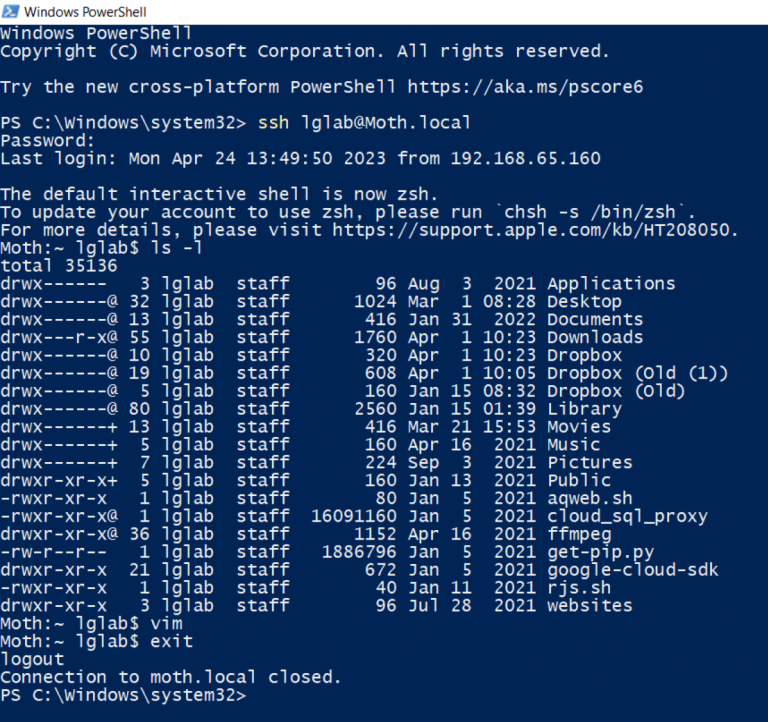
Step 3: Connect to Your IoT Device
With everything set up, it’s time to connect to your IoT device. Open a terminal and type:
ssh user@iot-device-ip
If everything is configured correctly, you should see a prompt asking you to log in. Once you’re in, you can start issuing commands to manage your device. For example, you can check the system status using:
sudo systemctl status
Or update the software with:
sudo apt update && sudo apt upgrade
Common SSH Remote IoT Commands
Now that you’re connected, let’s explore some of the most useful SSH Remote IoT Commands. These commands will help you manage your devices efficiently and troubleshoot any issues that arise.
1. File Management
Managing files is a fundamental part of IoT device management. Here are some essential commands:
ls: List files and directories.cd: Change directory.cp: Copy files.mv: Move or rename files.rm: Delete files.
2. System Monitoring
Keeping an eye on your IoT device’s performance is crucial. Use these commands to monitor system resources:
top: View real-time system processes.df: Check disk space usage.free: Display memory usage.
3. Network Configuration
IoT devices rely heavily on network connectivity. Use these commands to configure and troubleshoot network settings:
ifconfig: Display or configure network interfaces.ping: Test connectivity to another device.traceroute: Trace the path to a remote server.
Best Practices for Using SSH Remote IoT Commands
While SSH is incredibly powerful, it’s important to use it responsibly. Here are some best practices to keep in mind:
1. Use Strong Authentication
Always use public-key authentication instead of passwords. This not only enhances security but also simplifies the login process.
2. Limit User Access
Create separate user accounts for each person who needs access to your IoT devices. This way, you can monitor activity and revoke access if necessary.
3. Regularly Update Software
Keep your IoT devices and SSH server up to date with the latest patches and updates. This ensures that you’re protected against known vulnerabilities.
4. Monitor Logs
Regularly review your SSH logs to detect any suspicious activity. Most SSH servers log all connection attempts, making it easy to spot potential threats.
Advanced SSH Techniques for IoT Devices
Once you’ve mastered the basics, you can explore more advanced SSH techniques to take your IoT management to the next level.
1. Port Forwarding
Port forwarding allows you to securely access services running on your IoT device from anywhere in the world. For example, if you have a web server running on your device, you can use SSH to tunnel traffic to it without exposing it directly to the internet.
2. SSH Tunnels
SSH tunnels are a great way to bypass firewalls and access restricted networks. By creating a tunnel, you can securely connect to your IoT device even if it’s behind a corporate firewall.
3. Automated Scripts
Automating repetitive tasks can save you a ton of time. Use SSH to create scripts that perform tasks like backups, updates, and log rotations. For example, you can set up a cron job to run a script every night that backs up your device’s configuration files.
Case Studies: Real-World Applications of SSH Remote IoT Commands
Let’s look at some real-world examples of how SSH Remote IoT Commands are being used today.
1. Smart Home Automation
Many smart home systems rely on SSH to manage devices like thermostats, lighting, and security cameras. With SSH, homeowners can remotely control these devices and ensure they’re functioning properly.
2. Industrial Automation
In industrial settings, SSH is used to monitor and control machines, sensors, and other equipment. This allows engineers to troubleshoot issues in real-time and optimize production processes.
3. Environmental Monitoring
Researchers use SSH to collect data from remote sensors deployed in harsh environments, such as rainforests or deserts. SSH ensures that the data is transmitted securely and reliably, even in challenging conditions.
Conclusion
SSH Remote IoT Commands are a powerful tool for managing and securing your IoT devices. Whether you’re a tech enthusiast, a developer, or a business owner, understanding SSH can help you take control of your IoT ecosystem. By following best practices and exploring advanced techniques, you can unlock the full potential of SSH and create a safer, more efficient network of connected devices.
So, what are you waiting for? Start experimenting with SSH today and see how it can transform the way you interact with your IoT devices. And don’t forget to share your experiences in the comments below. Who knows? You might just inspire someone else to join the SSH revolution!
Table of Contents: